| SAFECode Guidance for Agile Practitioners |
| Written by Alex Armstrong |
| Monday, 30 July 2012 |
|
SAFECode, an industry consortium dedicated to assuring the security of software, has issued guidelines for incorporating security into the Agile coding process. Guidance for Agile Practitioners
The new guidelines come from the Software Assurance Forum for Excellence in Code (SAFECode) which was formed in 2007 by Microsoft, Juniper Networks, EMC, Corporation, SAP and Symantec as the first global, industry-led effort to identify and promote best practices for developing and delivering more secure and reliable software, hardware and services. Nokia joined SAFECode in 2008, Adobe was added in 2009 and last year Siemens became the newest member of the consortium.
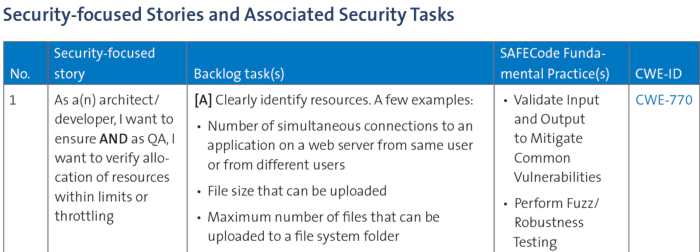
SAFECode's new paper "Practical Security Stories and Security Tasks for Agile Development Environments," provides practical software security guidance to Agile practitioners in the form of security-focused stories and security tasks they can easily integrate into their Agile-based development environments.
There are 36 of these stories, each of them associated with a set of SAFECode Fundamental Practices and the relevant entry in the Common Weakness Enumeration, a formal list or dictionary of common software weaknesses that can occur in software’s architecture, design, code or implementation that can lead to exploitable security vulnerabilities, maintained by the MITRE Corporation. A quick reference guide taken from the full paper is available as a pdf. According toStacy Simpson, SAFECode's policy and communications director, SAFECode has dedicated significant resources to evaluating and improving the secure development process based on the experiences of its members in real-world implementations,” Though presented in a list format, this paper is an extension of our commitment to our process-based approach. Our goal is to present key elements of that process in a way that can be more readily acted upon by Agile practitioners. We hope that this paper will be useful to organizations that use, or plan to use, Agile methods and wish to incorporate security or enhance existing security tasks in their development process.”
More InformationPractical Security Stories and Security Tasks for Agile Development Environments, To be informed about new articles on I Programmer, install the I Programmer Toolbar, subscribe to the RSS feed, follow us on, Twitter, Facebook, Google+ or Linkedin, or sign up for our weekly newsletter.
|
| Last Updated ( Sunday, 25 November 2018 ) |