| Using Microsoft Network Monitor 3.3 |
| Written by Mike James | |||
| Wednesday, 31 March 2010 | |||
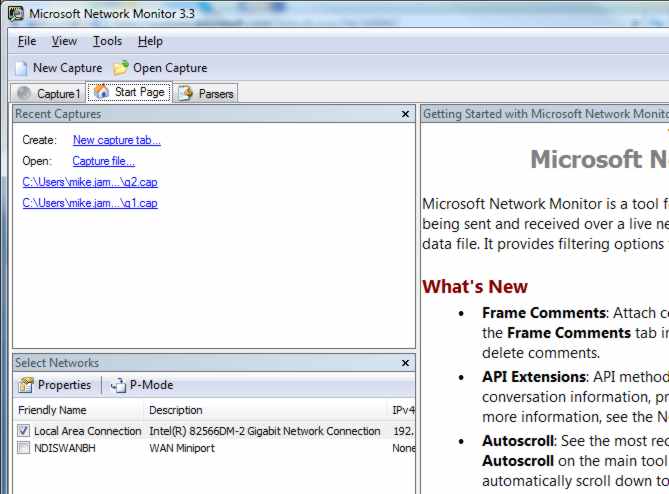
Page 1 of 2 Monitoring your network traffic at the packet level isn't something everyone wants or needs to do - but it is the most direct way of finding out what is going on. You can use it to track down the cause of network problems and to make sure that you don't have any network traffic that shouldn't be there. Using a monitor is also something of an education. For once you actually get to see all of the theory in action. Microsoft Network Monitor used to be included as part of a number of other packages but now you can downloaded it as a separate entity. The latest version 3.3 is also very much easier to use and more powerful than earlier versions. To follow this tutorial you need to download and install it. Search for Network Monitor on the Microsoft web site (www.Microsoft.com). My advice would be to install it on a client machine and one that has plenty of spare capacity and not critical to your work. The network monitor makes heavy demands on the hardware - both processor and disk - while in use and you need to find out more about how it works before using it on a production system. Once installed you can start it running but it is important to run it with full administrator privileges - simply right click on it and select Run as Administrator under Vista or Window 7. When the monitor first opens you need to check that there are network adaptors listed in the Select Networks window. If you don't see even one local area connection then either the machine isn't connected to a network or the monitor doesn't have the admin rights to access it. There is also the possibility that the network hardware isn't new enough to work with the monitor driver, but this is unlikely except in the case of some WiFi adaptors. WiFi network monitoring is a new feature of Network Monitor 3.3 so give it time to settle down.
Make sure you have some adaptors listed
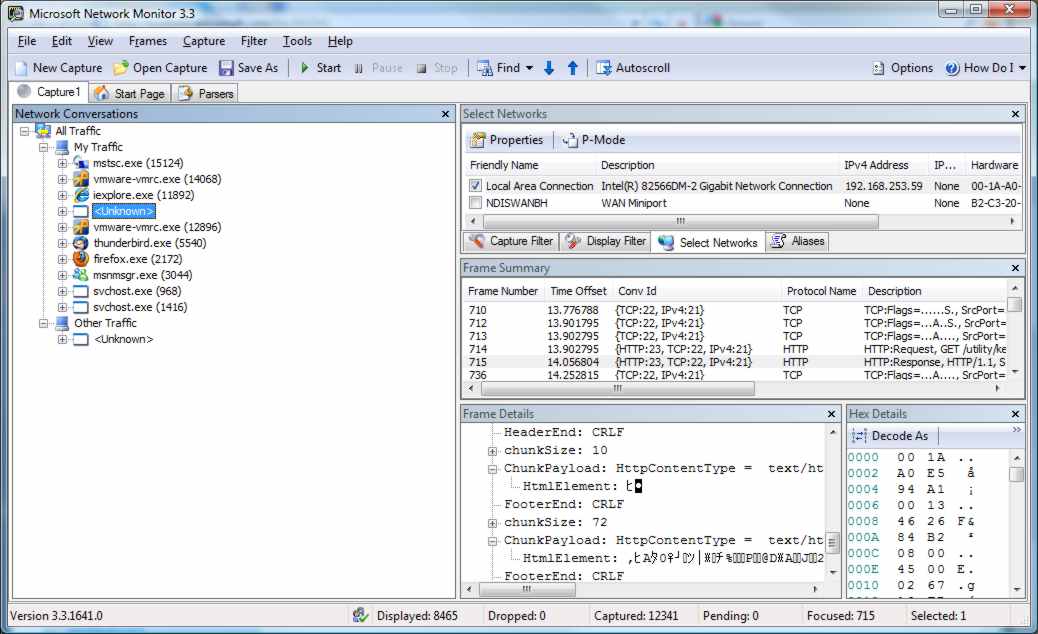
As long as you can see a network connection in the Select Networks window you can capture your first data. To do this just click the New Capture command and then click the Start button. You should see a list of network conversations appear in the Network Conversation window. After a few have accumulated, which should take 20 or 30 seconds depending on the network loading, click the Stop button to stop the capture. The Network conversation window shows a list of applications that have sent and received network data during the capture. Most of the programs that are listed should be known to you - iexplorer, firefox, msnmsgr and so on. Any applications listed that you don't know about could be an unwanted intruder but there are many perfectly legitimate services that you might well not recognise - svchost for example. You may also discover that you have some network traffic assigned to the "unknown" category. Again an unwanted intruder could be hiding in this list but there are many legitimate reasons why a system could be sending data packets from an unknown source.
The known and the unknown <ASIN:1593271794> <ASIN:0735625158> <ASIN:0470496649> |
|||
| Last Updated ( Sunday, 09 May 2010 ) |