| Print Me If You Dare - the Rise of Printer Malware |
| Written by Mike James | |||
| Sunday, 01 January 2012 | |||
|
The recent 28th Chaos Communications Congress has produced a number of interesting ideas, but a presentation of two hacks that turned printers into rogue machines was an eye opener for both programmer and IT manager. In his hour-long talk "Print Me If You Dare", Ang Cui demonstrated two printer hacks that are a clear sign that printers are no longer dumb enough to be ignored as part of the security problem. He showed that it was possible to load a program into the printer by embedding code into a document, or by direct connection to an infected PC.
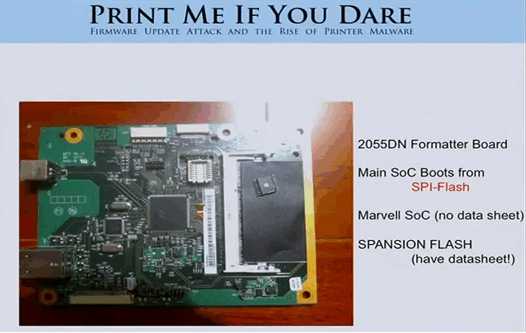
The attacks were all on HP printers and were the fruit of reverse engineering the firmware update mechanism. No doubt other printers could be attacked in the same way. Cui gave HP a month to issue patches to the firmware before making the details public and in theory the printers targeted should now be secure. However users should check because it is possible that a printer that was infected before the patch update will falsely report that it has been updated. You can see the full presentation here:
Previously the same exploits were misreported as being able to make a printer operate in such a way as to make it burst into flames or at least overheat. In practice, safety cutouts restrict the damage to singeing a piece of paper. So it seems exploding printers aren't a real threat but printers that make copies of all of your printed documents and send them to a public website are.
More Information
To be informed about new articles on I Programmer, subscribe to the RSS feed, follow us on Google+, Twitter, Linkedin or Facebook or sign up for our weekly newsletter.
Comments
or email your comment to: comments@i-programmer.info
|
|||
| Last Updated ( Sunday, 01 January 2012 ) |