| The tools of protest - WikiLeaks and Anonymous |
| Monday, 13 December 2010 | |||
|
A tool originally designed to stress test networks was used in last week's WikiLeaks denial of service protests. What is surprising is that at first look it doesn't seem fit for purpose in that it doesn't hide the identity of the people using it - thus rendering Anonymous far from anonymous.
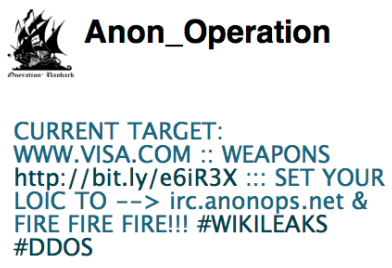
It isn't the place of a news service that specialises in everything programming to comment on political and social phenomena like WikiLeaks or the action to attack or defend their existence - except of course when there is a development angle. Anonymous is a group of "hacktivists" who organised a set of Denial of Service (DOS) attacks on the websites of companies who withdrew support for, or otherwise refused to be associated, with WikiLeaks. What is interesting is that this wasn't the usual "botnet" style of DOS; it was an organised opt-in protest. You went to the website, downloaded a tool called LOIC (Low Orbit Ion Cannon) and started it running on your machine. It was then used by the group to send IP packets to the website chosen for the attack. This much isn't entirely new. The new feature included in the WikiLeaks action is that LOIC was modified to allow it to be remote controlled via an IRC connection - the so called "Hive Mind" mode. This allowed the DOS attacks to be targeted and timed centrally. The history of LOIC is a long and complicated one. Basically it was invented as a network stress testing app (written in C#) and it simply floods the network with TCP/UDP packets or HTTP requests. It was quickly picked up as an easy to use DOS tool by a range of protesters - targets include Scientology, the RIAA in support of file sharing, and the opponents of WikiLeaks. The big problem is that LOIC is arguably not well engineered for the DOS task it is being used for. The addition of the IRC based Hive Mind is about the only specific DOS customisation added to the code base so far.
In a DOS attack created by a botnet the computers used in the attack have been hijacked by one form of malware or another and in this case there is no reason to hide their location. Each PC and its user involved in the attack has to be presumed innocent of the intent to cause a denial of service at the target. Hence there is no need to keep the source IP address of the packets sent in the attack hidden. Compare this with a co-operative protest implemented using LOIC. In this case the source IP addresses identify willing collaborators and hence people the authorities might well be interested in. What is more internet service providers are generally charged with the task of keeping IP logs for at least 6 months so there is plenty of time to do the analysis well after the DOS attack is over. In addition the attacked web server's logs will also identify the attacker's IP address. DOS attacks can be prosecuted under the Computer Fraud and Abuse Act in the US and via a specific DOS law in the UK for example. A study by the DACS group of the University of Twente has confirmed that LOIC hasn't been modified to include anonymity features - making Anonymous far from anonymous. As any programmer with any sockets or lower level net programming experience knows, it is very easy to put together code that will send any amount of data to any server. The difficult part is keeping the source of the packets hidden. The LOIC tool allows the user to set the port number mode of attack - TCP/UDP or HTTP, and the payload. The modified tool has the Hive Mind mode which allows these parameters to be set by a central server effectively creating something that looks like a voluntary botnet. As already mentioned the problem is that you don't run LOIC by accident, only by choice, and unfortunately it does nothing to hide the source IP address - why should a stress testing tool even try to? This raises the question of could it be done? For the technically minded programmer the idea that first occurs is IP spoofing - essentially writing a false IP address into the IP packet as the source address. This isn't difficult but it doesn't work for any protocol such as TCP and hence HTTP that needs to establish a connection by handshaking for the simple reason that you don't receive the return packets. So spoofing, while technically feasible, results in a very weak DOS attack. A better alternative would be to use an intermediate network - an anonymising network like tor or a VPN - to hide the IP address. A great idea but a DOS attack on a server would then route all of the traffic through the intermediate network and unless it was engineered to take the load it would fall over first. This is the reason tor doesn't allow P2P traffic for example. Perhaps it really is difficult to hide the identity of a mass of people self organising a DOS attack. This seems to be the nature of the Internet and not an inherent flaw in the design of LOIC. As the research paper states: Basically, for the average user of the LOIC tool, it is like he was asked to send a menace letter with a return address. More information: http://www.simpleweb.org/reports/loic-report.pdf
|
|||
| Last Updated ( Monday, 13 December 2010 ) |