| Navy Solicits Vulnerabilities |
| Written by Alex Armstrong | |||
| Wednesday, 17 June 2015 | |||
|
The US Navy is, or rather was last week, looking for contractors to supply it with zero-day vulnerabilities and similar - for what reasons? News of the availability of a 12-month contract, with three further 12-month options, was posted as Solicitation Number N0018915T0245 on FedBizOpps. This is a publicly accessible site where government agencies routinely post contracting opportunities.
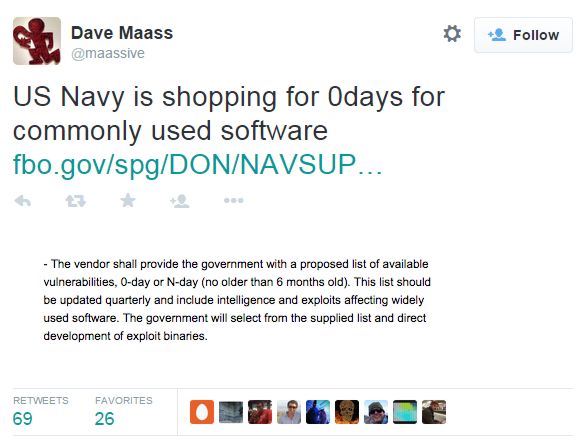
The details of what were required were: “access to vulnerability intelligence, exploit reports and operational exploit binaries affecting widely used and relied upon commercial software,” It specified the commercial products as including but not limited to: Microsoft, Adobe, JAVA, EMC, Novell, IBM, Android, Apple CISCO IOS, Linksys WRT, Linux and all others and that the vendor must be rated to Capability Maturity Model Integration (CMMI) Level 3 or greater. As captured in a tweet from Dava Mass, the solicatation stated:
“the vendor shall provide the government with a proposed list of available vulnerabilities, 0-day or N-day (no older than 6 months old). . . The government will select from the supplied list and direct development of exploit binaries.”
Shortly after this link was tweeted the page was removed but the Electronic Frontier Foundation recovered it from a Google cache so you can read still the solicitation in full (pdf).
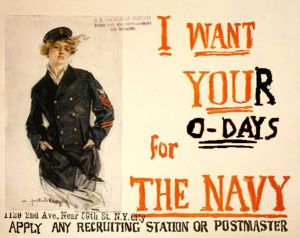
The EFF, which posted the above cartoon also commented: ...the fact that the United States government is looking for vendors to sell it software vulnerabilities isn’t news—we’ve known for some time that the government uses software vulnerabilities, sometimes known as zero-days, for offensive intelligence-gathering and espionage. . What’s more noteworthy is how little regard the government seems to have for the process of deciding to exploit vulnerabilities. As we’ve explained before, the decision to use a vulnerability for “offensive” purposes rather than disclosing it to the developer is one that prioritizes surveillance over the security of millions of users.
Whether the contract has already been awarded we don't know. But if you have the right level of expertise the navy may still need you.
More InformationDamn the Equities, Sell Your Zero-Days to the Navy! (EFF) Related ArticlesLOGJAM - Can The NSA Break 1024-bit DHM Keys? Earn United Airlines Award Miles For Finding Bugs What Does The NSA Think Of Cryptographers?
To be informed about new articles on I Programmer, install the I Programmer Toolbar, subscribe to the RSS feed, follow us on, Twitter, Facebook, Google+ or Linkedin, or sign up for our weekly newsletter.
Comments
or email your comment to: comments@i-programmer.info |
|||
| Last Updated ( Wednesday, 17 June 2015 ) |