| VS Code Extensions As Malware |
| Written by Mike James | |||
| Wednesday, 01 February 2023 | |||
|
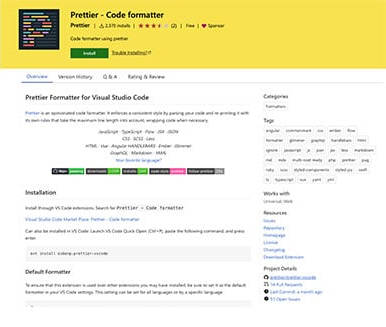
If you are popular enough then you wil draw the attention of attackers. A new study shows how easy it is to subvert the VS Code extensions supply chain. VS Code is popular - according to StackOverflow 75% of developers use it. As a raw code editor it isn't particularly impressive, but add to it the huge number of extensions that are available and you can assemble something workable and sometimes even something good. I use it because I can configure it to work with a range of languages in a range of situations on a range of platforms. Personally I'd prefer it if the core extensions were part of a configurable core program, but this is not how things are. Finding extensions is a big problem in terms of knowing who to trust. For most of the time I try to limit my use to well-known extensions, preferably authored by companies I know. Searching the 40K extensions for one that does the job and isn't just abandonedware or halfstartedware is difficult. Now it seems it is also dangerous. The problem is that extensions run will the same privileges as the user and there is no sandbox to keep the extension walled up in a prison. Once you realize this you can see how devastating an evil extension might be. The researchers from Aqua Team Nautilus decided to see if the threat was real. They created an extension that copied the look and feel of the Prettier code formatter and entered it into the Marketplace - the official source of extensions. What they created looks identical to the real entry until you notice that the URL is pretier - i.e. it's a case of typosquatting. Typosquatting is where you make use of user's inability to type accurately 100% of the time to get them to visit web pages which differ from the real thing by a spelling or punctuation error. As a dyslexic programmer you can see that I'm personally very vulnerable to this problem. And while I take extra care I don't think I'd ever spot it.
The problem is made worse by the fact that the extension name doesn't need to be unique - it's a display name. Other details are also easy to duplicate, including the project details and publisher. Harder to duplicate are the Unique Identifier which,yes, has to be unique, but again typosquatting to the rescue and esbenp.prettier-vscode becomes espenp.prettier-vscode - which is identical from my dyslexic point of view,. Of course, the number of installs and ratings can't be spoofed but as people download the faux extension they both go up. The researchers then go on to point out that Microsoft's attempts at verifying extensions isn't particularly convincing. For examp,e the blue Verified Author tick simply means that the author owns a domain - any domain. From here the attacker can opt to show the display name complete with the blue tick for the author's name. So did it work? Were real programemrs, some of whom are not dyslexic and hence not overly vulnerable to typosquatting, fooled? Yes they were. "In just under 48 hours, we got more than a thousand installs by active developers from all around the world! Now, imagine a real attacker (which would give the extension much more time to be active thus gain more credibility), with a real malicious extension, installed on many developers compromising many organizations. The impact of this is critical."
The researchers also point out that extensions make use of Node.js NPM as a package manager and any problems here will trickle down. They also point out that the same problems could occur with Visual Studio and Azure DevOps, but didn't pursue this angle. The part of the story that worries me is that extensions are not sandboxed. I go to a lot of trouble to avoid using software that is far better isolated from my development machine's environment. It seems I have to look more carefully in future. More InformationCan You Trust Your VSCode Extensions? Related ArticlesVisual Studio Code Adds Language Detection Python Extension For Visual Code Updated VS Code Improves Docker Support Visual Studio Online Is VS Code Open Source Visual Studio Code Without Trackers Launched To be informed about new articles on I Programmer, sign up for our weekly newsletter, subscribe to the RSS feed and follow us on Twitter, Facebook or Linkedin.
Comments
or email your comment to: comments@i-programmer.info |
|||
| Last Updated ( Wednesday, 01 February 2023 ) |