| Rust Fast And Safe |
| Written by Harry Fairhead | |||
| Wednesday, 15 June 2022 | |||
|
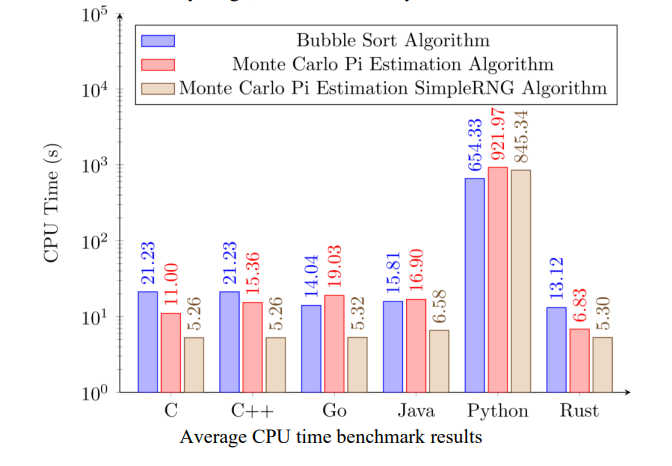
Rust is one of the few innovative languages threatening to shake up the old order, but is it really so good? A new research survey suggests that it really does seem to be both safer and faster, which is remarkable. The problem with evaluating any new language is that there is a halo effect. The early adopters mostly want to encourage other programmers to get on their bandwagon to keep it rolling. This means that you are likely to encounter strong arguments in favor of using the new language and only a few programmers speaking against the idea. What makes this worse is that the nay-sayers are generally less well informed about the language than its proponents and are easy to write off as ignorant of the the great ideas in the langauge. So it is with Rust. Its proponents have the louder and more persusive voicea, making it difficult to come to a conclusion. This makes informed and more neutral evaluation all the more valuable. A new study attempts to put what we know about Rust into context by presenting a survey of what we know: Does Rust deserve such increased attention? What is there in Rust that is attracting programmers to this new language? Safety and performance were among the very first promises of Rust, as was claimed by its early developers. Is Rust a safe language with high performance? Have these claims been achieved? First off it tries to find out if Rust really is as fast as the languages it is likley to be replacing. The surprising news is that Rust seems to be faster than C! It is certainly comparable to the other languages considered to be "fast". So there's no doubt that Rust is fastest over all three tasks, even if C/C++ shave off some milliseconds in the final one. The other side of the question is does this speed come at the expense of excessive memory usage:
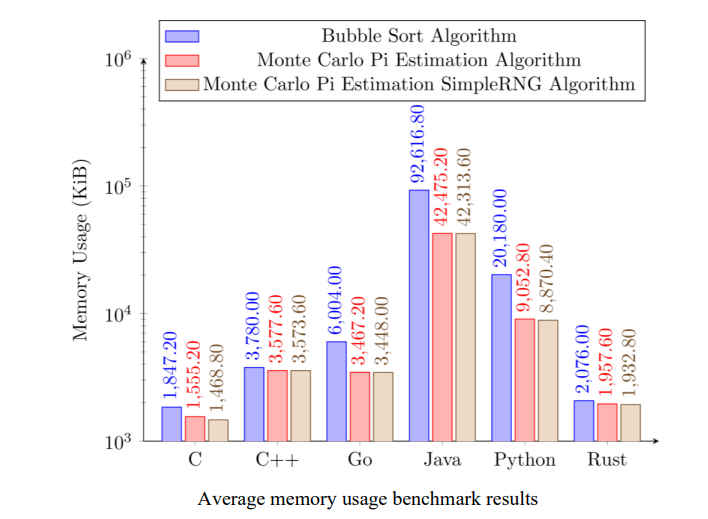
You can see Rust is only a little worse than C and much better than the rest. So is it safer? The paper gives a list of problems that Rust guards against: use after free, dereferencing a null pointer, double free, buffer overflow, buffer overread, and data races. The conclusion is that it does protect against all of these, as long as you don't resort to using the unsafe block. The problem here is that many have argued that Rust is so difficult to use that the unsafe block has to be resorted to more often than not. It is difficult to know if this is a significant fact in evaluating Rust and this survey doesn't address this problem. There isn't too much point in having a language that is safe if you don't opt out of its protection, but that protection makes it unsuable for most tasks. This is an area where we need more research. With Rust being allowed into the Linux kernel it is clearly a language that is on the rise. It is popular and promising, but is it mature enough to use for real? Clearly some well-informed programmers think so, but how often do they use unsafe?
More InformationRust: The Programming Language for Safety and Performance William Bugden, Ayman Alahmar Related ArticlesRust Is Safer But Do We Use It Safely Rust Bringing Greater Safety To Linux Rust Lang Releases 2024 Roadmap Rust Use Continues To Increase (Rust Survey 2022)
To be informed about new articles on I Programmer, sign up for our weekly newsletter, subscribe to the RSS feed and follow us on Twitter, Facebook or Linkedin.
Comments
or email your comment to: comments@i-programmer.info |
|||
| Last Updated ( Wednesday, 15 June 2022 ) |