| EU Bug Bounty - Software Security as a Civil Right |
| Written by Nikos Vaggalis | |||
| Wednesday, 09 January 2019 | |||
|
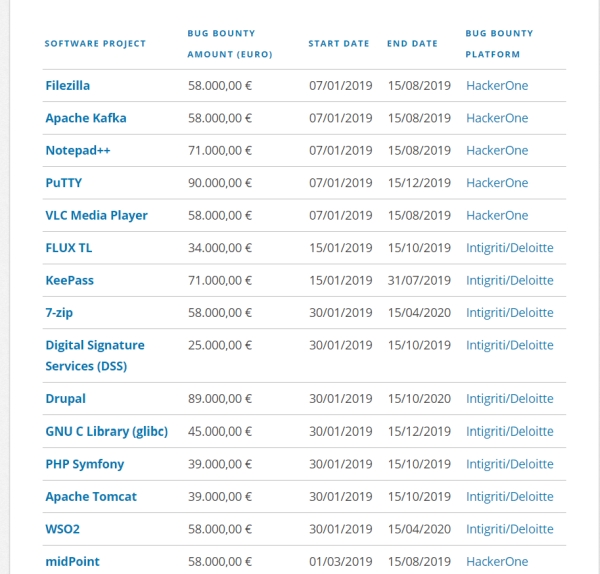
A State-sponsored bug bounty comes as refreshing news in that it shows that amongst the bureaucrats there are tech savvypeople who understand the true value of OSS software to society, and as such the impact when its security goes wrong. This EU initiative is part of the Free and Open Source Software Audit (FOSSA) project, thanks to Julia Reda MEP of the EU Pirate Party, who started the project thinking that enough is enough after severe vulnerabilities were discovered in key infrastructure components like OpenSSL. This prompted her to involve the EU Commission in contributing to the security of the Internet. It is amazing to think that the OpenSSL Software Foundation which is responsible for the maintenance of the OpenSSL library, the cornerstone of safe transactions on the Internet used by millions of websites and organizations, receives just $2000 of donation money per year and has only ONE full-time employee working on the library. All that was revealed after the discovery of the Heartbleed bug, something that finally shook the waters and motivated the big industry names to support the foundation with proper funding. Saying that, aren't Governments supposed to jump in and protect the public when the private sector cannot? That's the philosophy behind this novel initiative. A prime example of how deep OSS has infiltrated Governments, is that of Bulgaria whose state eGovernment agency SEGA is going to "award a contract for building the country’s open source code repository. The repository, to be based on Git, will be hosting source all software newly developed by or for Bulgaria’s public services".Everything is going to be released under a new kind of license, the European Union Public Licence (EUPL). But checking code written by a state and checking that of third party OSS applications used in governmental bureaus, are two different things. It's not apparent what the criteria for including an application on the bug bounty list are (probably the OSS most widely used in EU Governments or the EU Commission) but the list is diverse and sports a mix of end user desktop applications such as Filezilla, Notepad++ and 7-zip as well development tools, backends and frameworks such as Drupal, PHP Symfony, the WSO2 Integration Platform, as well as libraries like glibc.Talking about state-written code, the Digital Signature Services (DSS) open-source library is also included in the list.
This diversity goes to show that the security of desktop apps is considered at par with those of the serverside kind. In some cases it can be even more dangerous because desktop apps are consumed en masse, and when exploited it's not just some vague hacking attack happening on the Internet resulting in the leaking of credentials and personal information, but it is giving up full control of the users' PCs, therefore of their complete digital life. An example of that is the recently discovered vulnerability in one of the most popular OSS applications, 7-zip, which would allow for arbitrary code execution that could result in allowing an: "attacker to install programs; view, change, or delete data; or create new accounts with full user rights". In other words, it just needs a rigged compressed archive to wreak havoc. Let's not even consider the extent of the damage an app that is executed locally can have, taking into account the notorious, albeit propriety, examples of Adobe Flash and Java applets... Of course, discovering a bug, reporting it and creating a patch means nothing if users don't update to the patched version as soon as it's out. Therefore such efforts have to go hand in hand with enforcing Governmental wide update policies. Let's hope that this initiative will have a future, sustained by continuous and generous state funding. This would firmly establishing Julia Reda's perspective that, despite governments not having to pay for using OSS, they ought to be funding research into making it more secure for their public to use. Contrast this with the way in which the popular TrueCrypt application, used by millions of people in governments and homes alike, having to beg for money through crowdfunding in order to perform its own security audits. The German government eventually did run an audit, but that was a one-off action. Something more organized than that is called for. In the scheme that Julia Reda pushes forward, mission-critical OSS applications' audits should be state funded in order to serve the wider good. In other words, Software Security as a Civil right. More InformationIn January, the EU starts running Bug Bounties on Free and Open Source Software A Vulnerability in 7-Zip Could Allow for Arbitrary Code Execution Related ArticlesEver Increasing Need For Secure Programming Heartbleed - The Programmer's View Sharpen Your Hacking Skills With CTFLearn Hacktoberfest 2018 - Celebrate Open Source! Carnegie Mellon CyLab Challenge: Learn Hacking At School Hacksplaining - Learn Through Hacking
To be informed about new articles on I Programmer, sign up for our weekly newsletter, subscribe to the RSS feed and follow us on Twitter, Facebook or Linkedin.
Comments
or email your comment to: comments@i-programmer.info |
|||
| Last Updated ( Wednesday, 09 January 2019 ) |